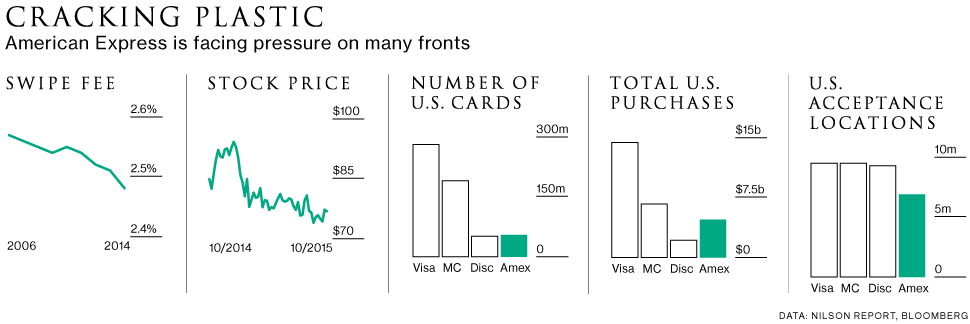
The amex decision sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset. Language translation plays a pivotal role in facilitating global communication, allowing diverse cultures to interact and understand one another. From its historical roots, where ancient texts were painstakingly deciphered, to the modern age where technology enhances the translation process, this discourse delves into the various dimensions of translation, examining its significance and the evolving landscape shaped by advancements in technology.
In the ever-evolving landscape of technology, the importance of digital security cannot be overstated. As individuals and organizations increasingly rely on the internet for their daily operations, the potential risks associated with cyber threats have surged. This article aims to shed light on the significance of digital security, explore the common threats faced, and provide practical measures to enhance protection against these risks.Digital security refers to the measures taken to protect electronic devices, networks, and data from unauthorized access, damage, or theft.
It encompasses a wide range of practices and technologies designed to safeguard sensitive information that is stored, processed, or transmitted electronically. In today’s digital age, where data breaches and cyber-attacks are becoming alarmingly common, understanding and implementing robust digital security measures is critical.One of the primary reasons for prioritizing digital security is the increasing incidence of cyber threats. Cybercriminals employ various tactics to exploit vulnerabilities in systems for financial gain, espionage, or even just for the thrill of it.
Some of the most common types of cyber threats include malware, phishing, ransomware, and denial-of-service attacks. Malware, short for malicious software, is a broad category that encompasses a range of harmful programs, including viruses, worms, and Trojans. These programs can disrupt the normal functioning of computers, steal sensitive information, or even take control of systems. To protect against malware, it is essential to install reputable antivirus software and regularly update it to defend against new threats.
Phishing is another prevalent cyber threat, often executed through deceptive emails or messages that appear to be from trustworthy sources. These messages typically trick individuals into providing personal information, such as usernames and passwords. To avoid falling victim to phishing attacks, one should always verify the sender’s identity before clicking on links or providing sensitive information. Ransomware has emerged as one of the most damaging forms of cyber threats in recent years.
This type of malware encrypts a victim’s files, rendering them inaccessible until a ransom is paid to the attacker. To mitigate the risks associated with ransomware, regular data backups and maintaining updated software are crucial. In the event of an attack, having backup copies of data can save organizations and individuals from significant loss. Denial-of-service (DoS) attacks aim to disrupt the normal functioning of a target server, service, or network by overwhelming it with a flood of traffic.
This can result in significant downtime and loss of revenue for businesses. Employing network security measures, such as firewalls and intrusion detection systems, can help prevent or mitigate the impact of DoS attacks.Given the variety and complexity of threats, establishing a comprehensive digital security strategy is paramount. Here are some effective measures that individuals and organizations can implement to bolster their digital security:
1. Use Strong Passwords
One of the simplest yet most effective ways to enhance security is by using strong, unique passwords for each account. A strong password typically includes a combination of letters, numbers, and special characters. Furthermore, using a password manager can help in generating and storing complex passwords securely.
2. Enable Two-Factor Authentication (2FA)
2FA adds an extra layer of security by requiring not only a password but also a second form of verification, such as a code sent to a mobile device. This ensures that even if a password is compromised, unauthorized access to the account is still restricted.
3. Regular Software Updates

Keeping software up to date is crucial, as developers frequently release patches to fix vulnerabilities. Enable automatic updates whenever possible to ensure that your devices are always protected against known threats.
4. Educate Employees
For organizations, educating employees about digital security best practices is essential. Regular training sessions can help staff recognize and respond to potential threats, such as phishing emails or suspicious attachments.
5. Implement Firewalls and Antivirus Solutions
Utilizing firewalls helps filter incoming and outgoing traffic, providing an additional layer of defense against cyber threats. Similarly, antivirus software can detect, quarantine, and remove malware before it causes harm.
6. Data Encryption
Encrypting sensitive data ensures that even if it is intercepted by cybercriminals, they cannot access it without the decryption key. This is particularly important for organizations dealing with sensitive customer information.
7. Regular Backups
Regularly backing up data to an external hard drive or cloud storage can significantly reduce the impact of data loss due to cyber-attacks. Ensure that backups are stored securely and tested for integrity.
8. Monitor Accounts and Systems
Regularly monitoring accounts and systems for unusual activity can help detect potential security breaches early. Implementing logging and alerting mechanisms can provide timely notifications of suspicious activities.

9. Limit Access to Sensitive Information
Restricting access to sensitive information based on the principle of least privilege ensures that only authorized personnel can access critical data. This minimizes the risk of internal breaches and data leaks.1
0. Incident Response Plan
Developing and maintaining an incident response plan prepares organizations to respond effectively to security breaches. Such a plan should Artikel the steps to take during an incident, who to contact, and how to mitigate damage.In conclusion, as we navigate through an increasingly digital world, the importance of digital security can never be underestimated. By understanding the various threats and implementing effective security measures, individuals and organizations can significantly reduce their risk of falling victim to cybercrimes.
It is essential to remain vigilant and proactive in safeguarding personal and organizational information, ensuring a secure digital environment for everyone. The cost of neglecting digital security is far greater than the investment required to protect against potential threats, making it a critical aspect of modern life in the digital age.
FAQ Explained
What is the primary role of a translator?
The primary role of a translator is to accurately convey the meaning of a source text into a target language, considering cultural nuances and context.
How has technology impacted translation?
Technology has significantly impacted translation by providing tools such as machine translation and software that assist translators, although it also presents challenges related to accuracy and context.
What types of translation exist?
Translation can be categorized into several types, including literary, technical, medical, legal, and audiovisual translation, each requiring specific skills and knowledge.
Are human translators still necessary with advances in machine translation?
Yes, human translators are still necessary as they provide essential context, cultural understanding, and nuanced interpretations that machines cannot fully replicate.
What are some common challenges in translation?
Common challenges in translation include dealing with idiomatic expressions, cultural references, ambiguity in language, and maintaining the tone of the original text.